Jamf Configuration
Business & Enterprise only
Note that our Jamf integration is limited to the Business and Enterprise product plans. See our pricing page for more information.
Background
Twingate integrates with Jamf so that admins can have it as a requirement to sign in to Twingate or access private resources. When Jamf is selected as a trust method within Device Security, it can be incorporated into Security Policies. Only Macs that are verified through the Jamf integration will be considered satisfying the Trusted Profile and thus be allowed to access private resources.
How it works
Twingate integrates with Jamf by utilizing the Jamf API to pull a list of devices managed under a specific customer’s tenant. Additionally, the Twingate client returns the device serial number and matches to a list of serial numbers from Jamf. If a device is verified to be managed by Jamf and has reported to Jamf within the last 7 days, it will be considered Jamf verified in Twingate.
Configuring the Jamf integration in Twingate
1. In Jamf, select which user credentials to use in Twingate
This user should have admin capabilities and have access to the API.
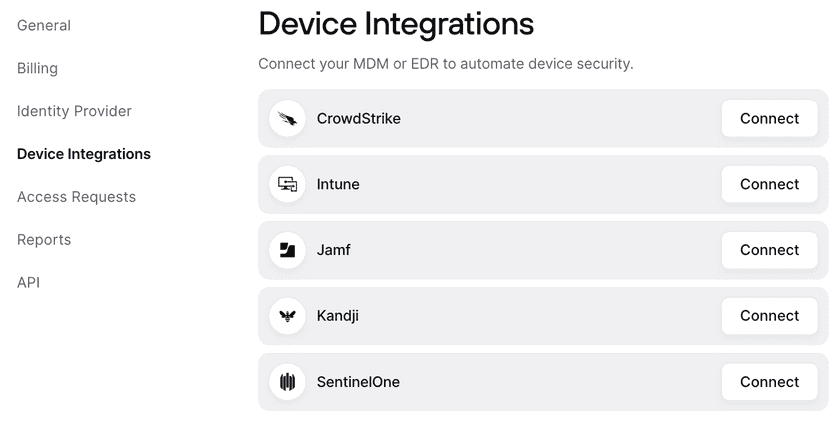
2. In Twingate, navigate to Settings and then select Device Integration
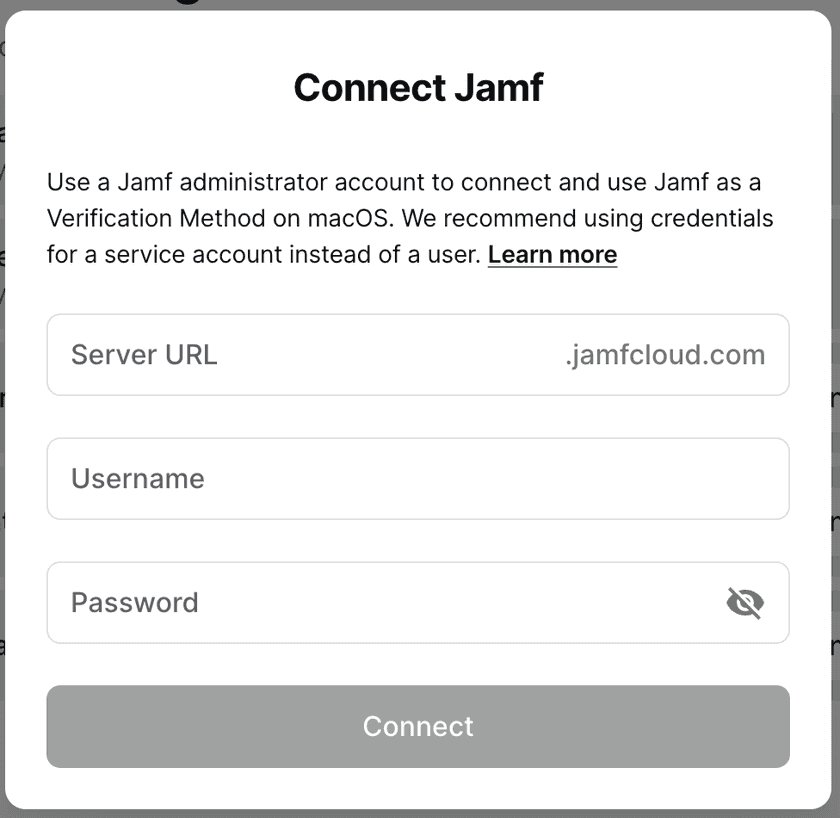
3. Select Connect next to Jamf and input your Jamf credentials
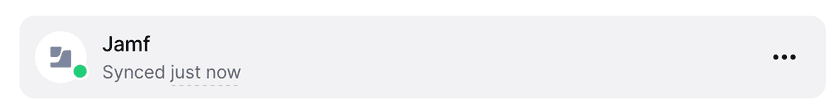
4. After the integration is configured, the Device Settings page will show the current status of the integration
Incorporating Jamf into Security Policies
After the Jamf integration has been configured, it can be configured into Device Security Trusted Profiles.
For macOS, create a Trusted Profile and require Jamf as a Trust Method. Only devices that have Jamf configured will satisfy the requirements of this Trusted Profile. The Trusted Profile can now be incorporated into Security Policies.
Troubleshooting
After the Jamf integration is set up, it can take up to 10 minutes for the initial sync to take place. During this time, devices may be missing the correct Jamf verification state and the Device Settings page will show the status as “Waiting to sync”. After this time, devices will correctly show the state on their device details page, and the Device Integration page will show the most recent sync time.
In the case of a recoverable error (e.g. the Jamf API is unresponsive), the Jamf integration may show that it has failed to sync. If so, the Device Settings page will show the time of last successful sync as well as the most recent failure to sync. When we are able to reach the Jamf API, the errors will be resolved automatically.
In the case of an unrecoverable error (e.g. the Jamf credentials are no longer valid is deleted or the permissions have been altered), the Jamf integration will stop attempting to connect. Admins will be notified via email that the Jamf integration needs attention. For these errors, we recommend reconfiguring the integration and inputting new API client information.
Last updated 9 months ago