Network Traffic
Twingate allows customers to view and export network activity on their remote networks. This can be useful for troubleshooting or investigatory purposes. Note that the only network activity that will be exported is traffic that flows through Connectors you have deployed. As Twingate is not a traditional VPN, it does not see other user traffic, which flows directly to the Internet.
Twingate provides several ways to view and export network traffic that flows through Connectors that you have deployed on your network:
- View network traffic in the Admin Console
- Manually exporting network traffic in CSV format via the Admin console
- Syncing network events in JSON format to an AWS S3 bucket
- Real-time connection logging, output directly by the Connector process
For more information on their the schemas for these events, see our network events schema page.
Viewing Network Traffic in the Admin Console
Network traffic can be viewed on either an individual User or Resource page.
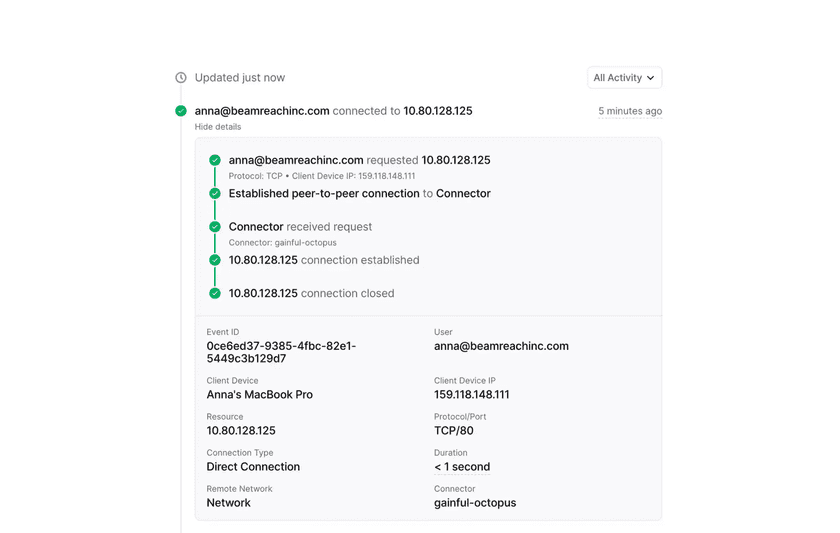
This view will show recent network traffic associated with this User or Resource. When clicking into a specific event, customers can see more details about the event. These additional details include the Resource IP address, protocol, connection type, and duration.
FAQs
Where is the IP of the client? This is currently not shown and will be added in a future update.
Why don’t I see access denied events? Due to the zero trust method Twingate uses, there is no way to distinguish between being denied access to a Resource and said Resource not existing at all, because the client only knows about Resources it has permissions to access. We are looking into how to address this in the future.
How long are events retained for? The minimum log retention period varies by plan:
- Starter: 24 hours
- Teams: 7 days
- Business: 30 days
- Enterprise: 12 months
Please refer to our pricing page for more details on the differences between our plans.
Last updated 3 months ago