How Do You Integrate Your DNS Filtering Service With Twingate?
Alex Marshall
•
Aug 19, 2022
DNS filtering adds an extra layer of security to your employees’ internet use. Here’s everything you need to know about integrating your DNS filtering service into the Twingate Zero Trust Network Access solution.
What is a DNS filter?
How users access the web can affect network security and reduce productivity. DNS filtering gives you control over the websites that users access, intentionally or unintentionally. A DNS filter acts before a browser or other web-aware application ever connects to malicious or unauthorized sites.
How does DNS work?
URLs are written so people can easily understand them. Computers, on the other hand, need to know a website’s numerical IP address. The Domain Name System is the global network that translates web domains into IP addresses.
When a user clicks a link, the browser contacts a DNS resolver which queries other servers in the DNS until it gets the website’s IP address. Users can only access the destination website after the DNS resolver hands the IP address to the browser.
DNS filters are features offered by some resolvers that refuse specific requests, thus preventing the browser from ever connecting to unsafe or inappropriate websites.
What are blocklists and allowlists?
DNS filters work by using blocklists. DNS service providers maintain lists of malicious domains and IP addresses. When the DNS filter receives a query for one of these prohibited internet destinations, it blocks the request. This approach depends on how quickly DNS service providers spot emerging security threats. Any delay in updating a DNS filter’s blocklist leaves a window of opportunity for security breaches.
Another approach is to use an allowlist. A DNS filter will reject any domain or IP address not explicitly included in this list. Although allowlists guarantee that users only access explicitly authorized destinations, this security comes at the expense of usability. Security teams must keep their allowlists synchronized with any network changes and deal with user exception requests.
Why is DNS filtering important?
The most important benefit of DNS filtering is preventing user devices from becoming attack vectors. Phishing attacks, malicious websites, and weaponized banner ads can expose your network with a single mouse click. DNS filtering blocks these attacks — if the attacks link to known domains. DNS filtering can also mitigate security breaches by preventing malware from contacting known command-and-control servers.
Companies also use DNS filters to improve productivity by keeping employees from using company systems to shop online or access social media. Similarly, DNS filtering can improve network performance by preventing access to bandwidth-hogging sites such as streaming services.
How do I enable DNS filtering services to secure public internet traffic outside of the Twingate network?
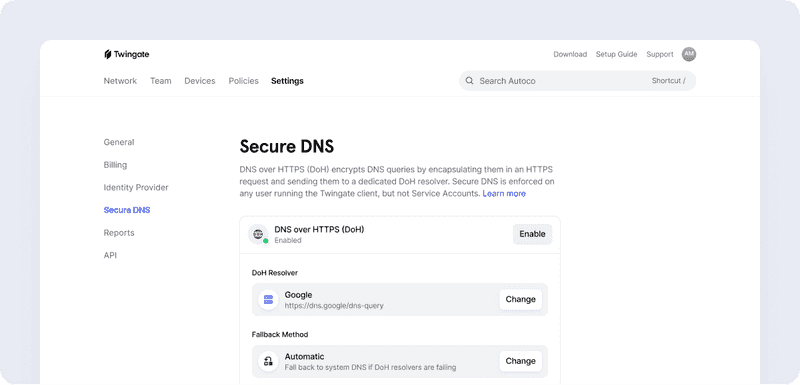
We recently announced Twingate’s Secure DNS, which lets you use DNS over HTTPS (DoH) for traffic outside the Twingate network, making DNS requests harder to intercept and modify. Secure DNS lets you specify the DoH resolver, whether provided by a third party or hosted on your network. If that resolver offers DNS filtering, it will screen every DNS request generated on user devices based upon specific configuration settings. Secure DNS expands our internet security vision, and integrated DNS filtering capabilities are coming soon.
Here are the steps for enabling DNS filtering services for traffic outside of the Twingate network.
1. Enable DoH for your Twingate account
Navigate to Settings > Secure DNS
Toggle the switch to enable DNS over HTTPS (DoH)
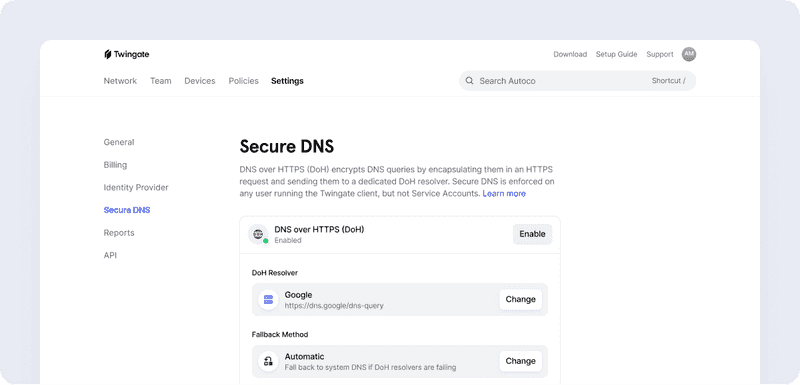
2. Specify the DoH resolver
Change the DoH Resolver to Custom and add the URL for your DNS filtering service (note: ensure that your DNS filtering provider supports DoH and what configuration is needed)
If you’re only interested in DoH capabilities, you can select one of our supported DoH resolvers: Cloudflare, Google, or OpenDNS.
3. Choose a Fallback Method
Should the DoH resolver fail, Twingate’s Client app can either fall back to the device’s default DNS resolver or deny all DNS requests.
Select the Fallback Method
Automatic - use default system DNS if resolvers are failing
Strict - keep DoH requirement, which will likely mean that all DNS resolution will fail
4. Manage exceptions
You can exempt select user groups from the DNS filter. If you created an Administrator group in Twingate, for example, placing that group on the exception list lets group members visit any domain or IP address.
Add any groups that should be exceptions and not require DoH
See how your DNS filter works with Twingate Secure DNS by joining our free Starter plan. Or contact us to learn more about our modern Zero Trust Network Access solution.
Rapidly implement a modern Zero Trust network that is more secure and maintainable than VPNs.
How Do You Integrate Your DNS Filtering Service With Twingate?
Alex Marshall
•
Aug 19, 2022
DNS filtering adds an extra layer of security to your employees’ internet use. Here’s everything you need to know about integrating your DNS filtering service into the Twingate Zero Trust Network Access solution.
What is a DNS filter?
How users access the web can affect network security and reduce productivity. DNS filtering gives you control over the websites that users access, intentionally or unintentionally. A DNS filter acts before a browser or other web-aware application ever connects to malicious or unauthorized sites.
How does DNS work?
URLs are written so people can easily understand them. Computers, on the other hand, need to know a website’s numerical IP address. The Domain Name System is the global network that translates web domains into IP addresses.
When a user clicks a link, the browser contacts a DNS resolver which queries other servers in the DNS until it gets the website’s IP address. Users can only access the destination website after the DNS resolver hands the IP address to the browser.
DNS filters are features offered by some resolvers that refuse specific requests, thus preventing the browser from ever connecting to unsafe or inappropriate websites.
What are blocklists and allowlists?
DNS filters work by using blocklists. DNS service providers maintain lists of malicious domains and IP addresses. When the DNS filter receives a query for one of these prohibited internet destinations, it blocks the request. This approach depends on how quickly DNS service providers spot emerging security threats. Any delay in updating a DNS filter’s blocklist leaves a window of opportunity for security breaches.
Another approach is to use an allowlist. A DNS filter will reject any domain or IP address not explicitly included in this list. Although allowlists guarantee that users only access explicitly authorized destinations, this security comes at the expense of usability. Security teams must keep their allowlists synchronized with any network changes and deal with user exception requests.
Why is DNS filtering important?
The most important benefit of DNS filtering is preventing user devices from becoming attack vectors. Phishing attacks, malicious websites, and weaponized banner ads can expose your network with a single mouse click. DNS filtering blocks these attacks — if the attacks link to known domains. DNS filtering can also mitigate security breaches by preventing malware from contacting known command-and-control servers.
Companies also use DNS filters to improve productivity by keeping employees from using company systems to shop online or access social media. Similarly, DNS filtering can improve network performance by preventing access to bandwidth-hogging sites such as streaming services.
How do I enable DNS filtering services to secure public internet traffic outside of the Twingate network?
We recently announced Twingate’s Secure DNS, which lets you use DNS over HTTPS (DoH) for traffic outside the Twingate network, making DNS requests harder to intercept and modify. Secure DNS lets you specify the DoH resolver, whether provided by a third party or hosted on your network. If that resolver offers DNS filtering, it will screen every DNS request generated on user devices based upon specific configuration settings. Secure DNS expands our internet security vision, and integrated DNS filtering capabilities are coming soon.
Here are the steps for enabling DNS filtering services for traffic outside of the Twingate network.
1. Enable DoH for your Twingate account
Navigate to Settings > Secure DNS
Toggle the switch to enable DNS over HTTPS (DoH)
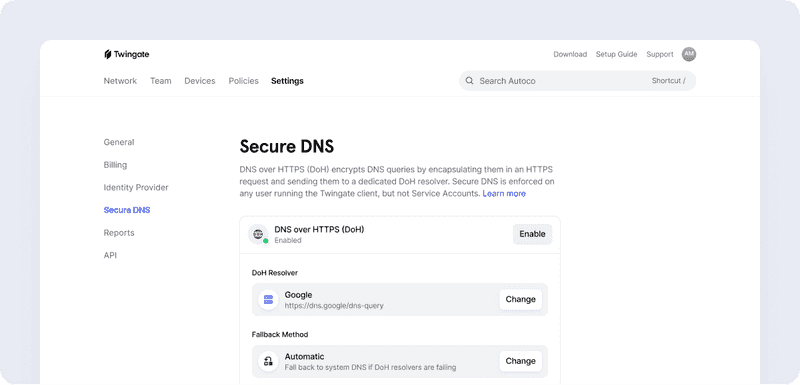
2. Specify the DoH resolver
Change the DoH Resolver to Custom and add the URL for your DNS filtering service (note: ensure that your DNS filtering provider supports DoH and what configuration is needed)
If you’re only interested in DoH capabilities, you can select one of our supported DoH resolvers: Cloudflare, Google, or OpenDNS.
3. Choose a Fallback Method
Should the DoH resolver fail, Twingate’s Client app can either fall back to the device’s default DNS resolver or deny all DNS requests.
Select the Fallback Method
Automatic - use default system DNS if resolvers are failing
Strict - keep DoH requirement, which will likely mean that all DNS resolution will fail
4. Manage exceptions
You can exempt select user groups from the DNS filter. If you created an Administrator group in Twingate, for example, placing that group on the exception list lets group members visit any domain or IP address.
Add any groups that should be exceptions and not require DoH
See how your DNS filter works with Twingate Secure DNS by joining our free Starter plan. Or contact us to learn more about our modern Zero Trust Network Access solution.
Rapidly implement a modern Zero Trust network that is more secure and maintainable than VPNs.
How Do You Integrate Your DNS Filtering Service With Twingate?
Alex Marshall
•
Aug 19, 2022
DNS filtering adds an extra layer of security to your employees’ internet use. Here’s everything you need to know about integrating your DNS filtering service into the Twingate Zero Trust Network Access solution.
What is a DNS filter?
How users access the web can affect network security and reduce productivity. DNS filtering gives you control over the websites that users access, intentionally or unintentionally. A DNS filter acts before a browser or other web-aware application ever connects to malicious or unauthorized sites.
How does DNS work?
URLs are written so people can easily understand them. Computers, on the other hand, need to know a website’s numerical IP address. The Domain Name System is the global network that translates web domains into IP addresses.
When a user clicks a link, the browser contacts a DNS resolver which queries other servers in the DNS until it gets the website’s IP address. Users can only access the destination website after the DNS resolver hands the IP address to the browser.
DNS filters are features offered by some resolvers that refuse specific requests, thus preventing the browser from ever connecting to unsafe or inappropriate websites.
What are blocklists and allowlists?
DNS filters work by using blocklists. DNS service providers maintain lists of malicious domains and IP addresses. When the DNS filter receives a query for one of these prohibited internet destinations, it blocks the request. This approach depends on how quickly DNS service providers spot emerging security threats. Any delay in updating a DNS filter’s blocklist leaves a window of opportunity for security breaches.
Another approach is to use an allowlist. A DNS filter will reject any domain or IP address not explicitly included in this list. Although allowlists guarantee that users only access explicitly authorized destinations, this security comes at the expense of usability. Security teams must keep their allowlists synchronized with any network changes and deal with user exception requests.
Why is DNS filtering important?
The most important benefit of DNS filtering is preventing user devices from becoming attack vectors. Phishing attacks, malicious websites, and weaponized banner ads can expose your network with a single mouse click. DNS filtering blocks these attacks — if the attacks link to known domains. DNS filtering can also mitigate security breaches by preventing malware from contacting known command-and-control servers.
Companies also use DNS filters to improve productivity by keeping employees from using company systems to shop online or access social media. Similarly, DNS filtering can improve network performance by preventing access to bandwidth-hogging sites such as streaming services.
How do I enable DNS filtering services to secure public internet traffic outside of the Twingate network?
We recently announced Twingate’s Secure DNS, which lets you use DNS over HTTPS (DoH) for traffic outside the Twingate network, making DNS requests harder to intercept and modify. Secure DNS lets you specify the DoH resolver, whether provided by a third party or hosted on your network. If that resolver offers DNS filtering, it will screen every DNS request generated on user devices based upon specific configuration settings. Secure DNS expands our internet security vision, and integrated DNS filtering capabilities are coming soon.
Here are the steps for enabling DNS filtering services for traffic outside of the Twingate network.
1. Enable DoH for your Twingate account
Navigate to Settings > Secure DNS
Toggle the switch to enable DNS over HTTPS (DoH)
2. Specify the DoH resolver
Change the DoH Resolver to Custom and add the URL for your DNS filtering service (note: ensure that your DNS filtering provider supports DoH and what configuration is needed)
If you’re only interested in DoH capabilities, you can select one of our supported DoH resolvers: Cloudflare, Google, or OpenDNS.
3. Choose a Fallback Method
Should the DoH resolver fail, Twingate’s Client app can either fall back to the device’s default DNS resolver or deny all DNS requests.
Select the Fallback Method
Automatic - use default system DNS if resolvers are failing
Strict - keep DoH requirement, which will likely mean that all DNS resolution will fail
4. Manage exceptions
You can exempt select user groups from the DNS filter. If you created an Administrator group in Twingate, for example, placing that group on the exception list lets group members visit any domain or IP address.
Add any groups that should be exceptions and not require DoH
See how your DNS filter works with Twingate Secure DNS by joining our free Starter plan. Or contact us to learn more about our modern Zero Trust Network Access solution.
Solutions
Solutions
The VPN replacement your workforce will love.
Solutions