How Google Cloud VPN Pricing Works & Affordable Alternatives
Stuart Loh
•
Oct 28, 2022
What is Google Cloud VPN?
Google Cloud VPN is a managed service offered by Google that lets organizations securely access the resources they host in their Google Cloud Platform (GCP) virtual private clouds (VPCs). Google Cloud VPN is used to securely connect a GCP VPC with other VPCs or non-GCP private networks (site-to-site or S2S connections).
It is important to note that Google Cloud VPN does not support users accessing VPC resources (point-to-site or P2S connections). If you need a solution for remotely accessing your VPC, see the “Alternatives to Google Cloud VPN‚ section below.
It’s possible to set up your own VPN server within GCP, but the selling point of Google Cloud VPN is that it streamlines the involved process of setting up, configuring and deploying a VPN server.
While the technical process of setting up a Google Cloud VPN may be easier, it is a paid service that comes with a complicated pricing model. Whereas the costs of running and managing your own VPN server software are normally pretty clear, Google Cloud VPN’s pricing is based on a confusing array of variables which make it challenging to determine expected costs for budgeting purposes.
In this article, we’ll break down how Google Cloud VPN’s pricing works, provide a convenient cost calculator, and review some alternatives to Google Cloud VPN.
How Google Cloud VPN Pricing Works
You will incur Google Cloud VPN charges for 3 different items:
Cloud VPN gateway charge (time-based)
Number of non-tunnel external IP addresses assigned to a VPN gateway (time-based)
Data transfer charges for IPsec egress traffic (usage-based)
Let’s dive into each item and understand what they are and what drives their cost.
VPN Gateway Charge
Google charges for each VPN gateway you have based on the number of tunnels you have attached to that gateway. A tunnel in this case is a secure connection that is established between a VPN gateway, and another VPN gateway associated with a different private network (which could be another GCP VPC or a non-GCP private network, such as an on-premises office network). Additionally, Google will not bill for tunnels if they are in certain states (for example, a tunnel is not billed while it is in a provisioning or deprovisioning state).
For each tunnel, Google charges an hourly fee that is based on the Google Cloud region in which the VPN gateway is located.
Google also offers what it calls “high availability‚ (HA) VPN gateways. These gateways have a 99.99% availability SLA, but require a pair of tunnels to be set up on each gateway. This means that if you are connecting two VPCs together, you will need a total of 4 tunnels (2 tunnels attached to each HA VPN gateway in each VPC). Each HA VPN gateway must also be in the same Google Cloud region.
Each VPN tunnel: $0.05 to $0.075 per hour
Non-tunnel External IP Addresses
Google also charges for each external IP address assigned to a VPN gateway, but only if the IP address is not used as a public IP address for a Cloud VPN tunnel. (Google also does not charge for static external IP addresses that are assigned to forwarding rules that send traffic to the VPN gateway.)
For each external IP address, Google charges an hourly fee that is based on their standard external IP address pricing, which is:
Static and ephemeral IP addresses used on standard VM instances: $0.004 per hour
Static and ephemeral IP addresses used on preemptible VM instances: $0.002 per hour
Preemptible VM instances are cheaper VMs that use excess Compute capacity within Google Cloud, but are subject to being stopped if the excess computing power is needed by standard VM instances.
Currently, charges are the same regardless of the region that the VPN gateway is located in, but Google may introduce differentiated pricing in future. In summary:
Each non-tunnel external IP address: $0.002 to $0.004 per hour
Egress Data Transfer Charges
Google charges data transfer fees for egress traffic (traffic exiting a VPC via a Cloud VPN gateway). Two pricing schemes exist depending on the destination of that traffic: outbound traffic destined for another Cloud VPN gateway uses VM-VM egress pricing rates, and outbound traffic destined for a VPN gateway outside of Google Cloud uses internet egress pricing rates. Fees are attributed to the project of the VM that is sending the traffic.
If the source and destination Cloud VPN gateways are in the same Google Cloud region, egress traffic is billed as traffic between zones in the same region.
VM-VM egress pricing: VM-VM traffic is priced on a per GB basis, and the rate is determined by the region of the source VPN gateway and the region of the destination VPN gateway, as well as whether internal IP addresses or external IP addresses are being used. (Note that the IP address of the destination VPN gateway determines the destination location, not the IP address of the destination VM a connection is ultimately intended for.)
Egress traffic is cheapest when it is sent to the same Google Cloud zone or region. Inter-regional egress traffic within the same continent is more expensive ($0.01 to $0.08 per GB), and intercontinental egress traffic is more expensive still ($0.08 to $0.15 per GB).
Amount of VM-VM egress data transferred: Up to $0.15 per GB
Internet egress pricing: Google offers two tiers of internet egress pricing - Standard and Premium (Premium is used as the default unless you specify Standard explicitly). Both tiers price using different approaches.
Premium Tier pricing charges a per GB rate which is based on: (1) the region the source VPN gateway is located in, (2) the location of the traffic’s destination, and (3) the aggregate monthly bandwidth used, with lower rates available with greater monthly bandwidth use.
For example, if you have a Cloud VPN gateway in the Las Vegas region (us-west4), the first 1 TB of egress traffic bound for Australia in a month is charged at $0.19 per GB, and the next 9 TB is charged at $0.18 per GB.
Standard Tier pricing charges a per GB rate which is based on: (1) the region the source VPN gateway is located in, and (2) the aggregate monthly bandwidth used, with lower rates available with greater monthly bandwidth use.
For example, if you have a Cloud VPN gateway in the Tokyo region (asia-northeast1), the first 10 TB of egress traffic in a month is charged at $0.11 per GB (regardless of destination), and the next 140 TB is charged a $0.075 per GB.
(As of the date of publication, we note there is an inconsistency with units in Google’s pricing page for the Standard Tier - it mentions that egress pricing is per GiB delivered, but the table and everywhere else on the page references GB, so we have assumed GB is the correct unit. GBs are smaller than GiBs.)
Amount of internet egress data transferred (premium tier): $0.08 to $0.23 per GB
Amount of internet egress data transferred (standard tier): $0.045 to $0.12 per GB
Google Cloud VPN Pricing Calculator
Because there are a lot of variables to account for when working out pricing, we’ve made this Google Cloud VPN Pricing Calculator to help you estimate the fees you can expect to pay for your Cloud VPN.
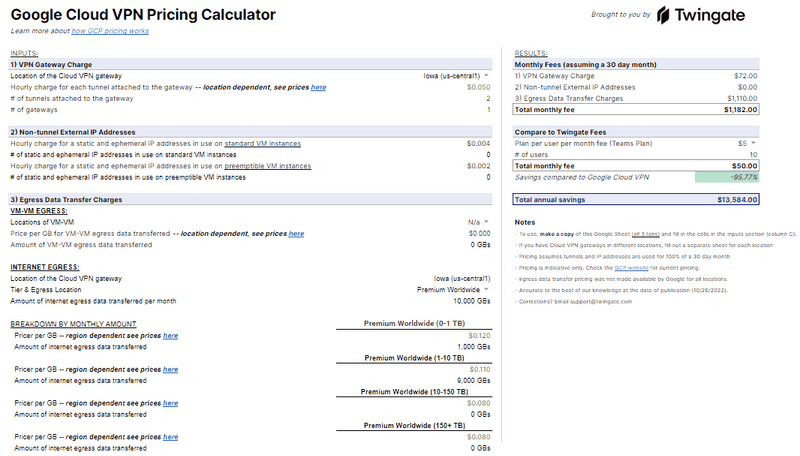
Google Cloud VPN Pricing Calculator
We note that pricing changes from time to time. The information in this article is accurate to the best of our knowledge at the date of writing, but you should check the Google Cloud website for the most up to date pricing.
Summary
Google Cloud VPN cannot be used as a P2S VPN server. If you use it as a P2P VPN server, the charges you can expect to pay for Google Cloud VPN include:
Hourly fees for each VPN tunnel attached to a Cloud VPN gateway
Hourly fees for each non-tunnel external IP address assigned to a Cloud VPN gateway
Bandwidth fees for egress traffic from the VPC the VPN gateway is located in
Alternatives to Google Cloud VPN
Google Cloud VPN is not your only option for establishing a secure way to access your GCP VPC environments. Moreover, one of the major limitations of Google Cloud VPN is that it cannot currently be used as a point-to-site VPN gateway that allows clients to securely connect into a GCP VPC.
Google Cloud Marketplace Products
The Google Cloud Marketplace contains a range of service providers who offer their own VPN software solutions that integrate with GCP. If you are looking for a P2S VPN gateway for Google Cloud, Google suggests in its documentation that customers may choose a marketplace vendor solution if a P2S VPN gateway is needed.
Each vendor offers their own pricing model, and a common deployment model is to offer VPN server software within a virtual machine (VM) that you can deploy into your VPC. OpenVPN Access Server is one such P2S-capable solution that is made available as an appliance. A subscription to the solution is purchased directly from OpenVPN and fees are based on the number of VPN connections needed, with a 5 connection minimum, and can be billed monthly or annually.
Manually Installed Products
On the other side of the spectrum, you could manually install and configure a software solution on a VM within your GCP VPC. Although there may be no software licensing fee associated with this route (such as for open source software) or perhaps a one-off payment for a perpetual license (for commercial software), it does require a lot more effort and expertise in terms of setup and maintenance. Additionally, support may not be provided, so you may have to seek third party help if you run into problems (either paid, or from free sources like community forums).
Zero Trust Alternative
If you are ultimately looking for a remote access solution, also consider Zero Trust Network Access products that aren’t based on VPN technology, such as Twingate. Twingate can be installed in a GCP VPC with a single line of code. Additionally, deployment can be automated in a variety of ways.
Another advantage of Twingate is that, unlike VPN technologies, there’s no concept of setting up site-to-site VPN tunnels to establish connectivity to your various network subnets. That reduces deployment complexity, as well as pricing complexity.
Zero Trust solutions have distinct security advantages over VPNs as well.
Twingate’s Pricing Model
A key benefit of using Twingate to secure remote access to your GCP environment is that the pricing model is straightforward. Twingate’s pricing is based on a per user flat fee model. That means costs are predictable - and you don’t need a spreadsheet to work them out!
The only variables that impact Twingate’s pricing are the number of users you have, the months or years you subscribe to the service (depending on whether you are billed monthly or annually), and the Twingate plan you select (Teams, Business or Enterprise). Subject to our Fair Use Policy, Twingate does not charge for bandwidth used or time connected. We even offer a free Starter plan if you want to try us out or if you only have a limited amount of infrastructure you need to secure.
If you use Twingate with non-GCP environments, support for GCP comes at no extra cost. In fact, Twingate secures access to all major types of environments (AWS, GCP, Azure, and on-premises) you may have for the same fee, and the setup process is similar for each environment.
Simplify Your GCP Secure Remote Access Needs
Twingate aims to provide the security benefits of a non-VPN Zero Trust solution while making deployment and management of that solution as simple as possible. Part of this is providing a simple to understand pricing model that won’t unexpectedly blow out your budget.
Contact us to learn more about how easy and cost effective implementing a modern zero trust solution can be.
Rapidly implement a modern Zero Trust network that is more secure and maintainable than VPNs.
How Google Cloud VPN Pricing Works & Affordable Alternatives
Stuart Loh
•
Oct 28, 2022
What is Google Cloud VPN?
Google Cloud VPN is a managed service offered by Google that lets organizations securely access the resources they host in their Google Cloud Platform (GCP) virtual private clouds (VPCs). Google Cloud VPN is used to securely connect a GCP VPC with other VPCs or non-GCP private networks (site-to-site or S2S connections).
It is important to note that Google Cloud VPN does not support users accessing VPC resources (point-to-site or P2S connections). If you need a solution for remotely accessing your VPC, see the “Alternatives to Google Cloud VPN‚ section below.
It’s possible to set up your own VPN server within GCP, but the selling point of Google Cloud VPN is that it streamlines the involved process of setting up, configuring and deploying a VPN server.
While the technical process of setting up a Google Cloud VPN may be easier, it is a paid service that comes with a complicated pricing model. Whereas the costs of running and managing your own VPN server software are normally pretty clear, Google Cloud VPN’s pricing is based on a confusing array of variables which make it challenging to determine expected costs for budgeting purposes.
In this article, we’ll break down how Google Cloud VPN’s pricing works, provide a convenient cost calculator, and review some alternatives to Google Cloud VPN.
How Google Cloud VPN Pricing Works
You will incur Google Cloud VPN charges for 3 different items:
Cloud VPN gateway charge (time-based)
Number of non-tunnel external IP addresses assigned to a VPN gateway (time-based)
Data transfer charges for IPsec egress traffic (usage-based)
Let’s dive into each item and understand what they are and what drives their cost.
VPN Gateway Charge
Google charges for each VPN gateway you have based on the number of tunnels you have attached to that gateway. A tunnel in this case is a secure connection that is established between a VPN gateway, and another VPN gateway associated with a different private network (which could be another GCP VPC or a non-GCP private network, such as an on-premises office network). Additionally, Google will not bill for tunnels if they are in certain states (for example, a tunnel is not billed while it is in a provisioning or deprovisioning state).
For each tunnel, Google charges an hourly fee that is based on the Google Cloud region in which the VPN gateway is located.
Google also offers what it calls “high availability‚ (HA) VPN gateways. These gateways have a 99.99% availability SLA, but require a pair of tunnels to be set up on each gateway. This means that if you are connecting two VPCs together, you will need a total of 4 tunnels (2 tunnels attached to each HA VPN gateway in each VPC). Each HA VPN gateway must also be in the same Google Cloud region.
Each VPN tunnel: $0.05 to $0.075 per hour
Non-tunnel External IP Addresses
Google also charges for each external IP address assigned to a VPN gateway, but only if the IP address is not used as a public IP address for a Cloud VPN tunnel. (Google also does not charge for static external IP addresses that are assigned to forwarding rules that send traffic to the VPN gateway.)
For each external IP address, Google charges an hourly fee that is based on their standard external IP address pricing, which is:
Static and ephemeral IP addresses used on standard VM instances: $0.004 per hour
Static and ephemeral IP addresses used on preemptible VM instances: $0.002 per hour
Preemptible VM instances are cheaper VMs that use excess Compute capacity within Google Cloud, but are subject to being stopped if the excess computing power is needed by standard VM instances.
Currently, charges are the same regardless of the region that the VPN gateway is located in, but Google may introduce differentiated pricing in future. In summary:
Each non-tunnel external IP address: $0.002 to $0.004 per hour
Egress Data Transfer Charges
Google charges data transfer fees for egress traffic (traffic exiting a VPC via a Cloud VPN gateway). Two pricing schemes exist depending on the destination of that traffic: outbound traffic destined for another Cloud VPN gateway uses VM-VM egress pricing rates, and outbound traffic destined for a VPN gateway outside of Google Cloud uses internet egress pricing rates. Fees are attributed to the project of the VM that is sending the traffic.
If the source and destination Cloud VPN gateways are in the same Google Cloud region, egress traffic is billed as traffic between zones in the same region.
VM-VM egress pricing: VM-VM traffic is priced on a per GB basis, and the rate is determined by the region of the source VPN gateway and the region of the destination VPN gateway, as well as whether internal IP addresses or external IP addresses are being used. (Note that the IP address of the destination VPN gateway determines the destination location, not the IP address of the destination VM a connection is ultimately intended for.)
Egress traffic is cheapest when it is sent to the same Google Cloud zone or region. Inter-regional egress traffic within the same continent is more expensive ($0.01 to $0.08 per GB), and intercontinental egress traffic is more expensive still ($0.08 to $0.15 per GB).
Amount of VM-VM egress data transferred: Up to $0.15 per GB
Internet egress pricing: Google offers two tiers of internet egress pricing - Standard and Premium (Premium is used as the default unless you specify Standard explicitly). Both tiers price using different approaches.
Premium Tier pricing charges a per GB rate which is based on: (1) the region the source VPN gateway is located in, (2) the location of the traffic’s destination, and (3) the aggregate monthly bandwidth used, with lower rates available with greater monthly bandwidth use.
For example, if you have a Cloud VPN gateway in the Las Vegas region (us-west4), the first 1 TB of egress traffic bound for Australia in a month is charged at $0.19 per GB, and the next 9 TB is charged at $0.18 per GB.
Standard Tier pricing charges a per GB rate which is based on: (1) the region the source VPN gateway is located in, and (2) the aggregate monthly bandwidth used, with lower rates available with greater monthly bandwidth use.
For example, if you have a Cloud VPN gateway in the Tokyo region (asia-northeast1), the first 10 TB of egress traffic in a month is charged at $0.11 per GB (regardless of destination), and the next 140 TB is charged a $0.075 per GB.
(As of the date of publication, we note there is an inconsistency with units in Google’s pricing page for the Standard Tier - it mentions that egress pricing is per GiB delivered, but the table and everywhere else on the page references GB, so we have assumed GB is the correct unit. GBs are smaller than GiBs.)
Amount of internet egress data transferred (premium tier): $0.08 to $0.23 per GB
Amount of internet egress data transferred (standard tier): $0.045 to $0.12 per GB
Google Cloud VPN Pricing Calculator
Because there are a lot of variables to account for when working out pricing, we’ve made this Google Cloud VPN Pricing Calculator to help you estimate the fees you can expect to pay for your Cloud VPN.
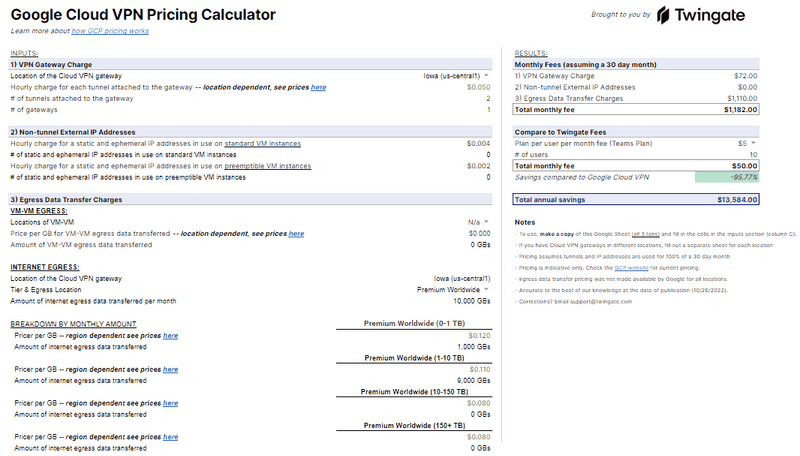
Google Cloud VPN Pricing Calculator
We note that pricing changes from time to time. The information in this article is accurate to the best of our knowledge at the date of writing, but you should check the Google Cloud website for the most up to date pricing.
Summary
Google Cloud VPN cannot be used as a P2S VPN server. If you use it as a P2P VPN server, the charges you can expect to pay for Google Cloud VPN include:
Hourly fees for each VPN tunnel attached to a Cloud VPN gateway
Hourly fees for each non-tunnel external IP address assigned to a Cloud VPN gateway
Bandwidth fees for egress traffic from the VPC the VPN gateway is located in
Alternatives to Google Cloud VPN
Google Cloud VPN is not your only option for establishing a secure way to access your GCP VPC environments. Moreover, one of the major limitations of Google Cloud VPN is that it cannot currently be used as a point-to-site VPN gateway that allows clients to securely connect into a GCP VPC.
Google Cloud Marketplace Products
The Google Cloud Marketplace contains a range of service providers who offer their own VPN software solutions that integrate with GCP. If you are looking for a P2S VPN gateway for Google Cloud, Google suggests in its documentation that customers may choose a marketplace vendor solution if a P2S VPN gateway is needed.
Each vendor offers their own pricing model, and a common deployment model is to offer VPN server software within a virtual machine (VM) that you can deploy into your VPC. OpenVPN Access Server is one such P2S-capable solution that is made available as an appliance. A subscription to the solution is purchased directly from OpenVPN and fees are based on the number of VPN connections needed, with a 5 connection minimum, and can be billed monthly or annually.
Manually Installed Products
On the other side of the spectrum, you could manually install and configure a software solution on a VM within your GCP VPC. Although there may be no software licensing fee associated with this route (such as for open source software) or perhaps a one-off payment for a perpetual license (for commercial software), it does require a lot more effort and expertise in terms of setup and maintenance. Additionally, support may not be provided, so you may have to seek third party help if you run into problems (either paid, or from free sources like community forums).
Zero Trust Alternative
If you are ultimately looking for a remote access solution, also consider Zero Trust Network Access products that aren’t based on VPN technology, such as Twingate. Twingate can be installed in a GCP VPC with a single line of code. Additionally, deployment can be automated in a variety of ways.
Another advantage of Twingate is that, unlike VPN technologies, there’s no concept of setting up site-to-site VPN tunnels to establish connectivity to your various network subnets. That reduces deployment complexity, as well as pricing complexity.
Zero Trust solutions have distinct security advantages over VPNs as well.
Twingate’s Pricing Model
A key benefit of using Twingate to secure remote access to your GCP environment is that the pricing model is straightforward. Twingate’s pricing is based on a per user flat fee model. That means costs are predictable - and you don’t need a spreadsheet to work them out!
The only variables that impact Twingate’s pricing are the number of users you have, the months or years you subscribe to the service (depending on whether you are billed monthly or annually), and the Twingate plan you select (Teams, Business or Enterprise). Subject to our Fair Use Policy, Twingate does not charge for bandwidth used or time connected. We even offer a free Starter plan if you want to try us out or if you only have a limited amount of infrastructure you need to secure.
If you use Twingate with non-GCP environments, support for GCP comes at no extra cost. In fact, Twingate secures access to all major types of environments (AWS, GCP, Azure, and on-premises) you may have for the same fee, and the setup process is similar for each environment.
Simplify Your GCP Secure Remote Access Needs
Twingate aims to provide the security benefits of a non-VPN Zero Trust solution while making deployment and management of that solution as simple as possible. Part of this is providing a simple to understand pricing model that won’t unexpectedly blow out your budget.
Contact us to learn more about how easy and cost effective implementing a modern zero trust solution can be.
Rapidly implement a modern Zero Trust network that is more secure and maintainable than VPNs.
How Google Cloud VPN Pricing Works & Affordable Alternatives
Stuart Loh
•
Oct 28, 2022
What is Google Cloud VPN?
Google Cloud VPN is a managed service offered by Google that lets organizations securely access the resources they host in their Google Cloud Platform (GCP) virtual private clouds (VPCs). Google Cloud VPN is used to securely connect a GCP VPC with other VPCs or non-GCP private networks (site-to-site or S2S connections).
It is important to note that Google Cloud VPN does not support users accessing VPC resources (point-to-site or P2S connections). If you need a solution for remotely accessing your VPC, see the “Alternatives to Google Cloud VPN‚ section below.
It’s possible to set up your own VPN server within GCP, but the selling point of Google Cloud VPN is that it streamlines the involved process of setting up, configuring and deploying a VPN server.
While the technical process of setting up a Google Cloud VPN may be easier, it is a paid service that comes with a complicated pricing model. Whereas the costs of running and managing your own VPN server software are normally pretty clear, Google Cloud VPN’s pricing is based on a confusing array of variables which make it challenging to determine expected costs for budgeting purposes.
In this article, we’ll break down how Google Cloud VPN’s pricing works, provide a convenient cost calculator, and review some alternatives to Google Cloud VPN.
How Google Cloud VPN Pricing Works
You will incur Google Cloud VPN charges for 3 different items:
Cloud VPN gateway charge (time-based)
Number of non-tunnel external IP addresses assigned to a VPN gateway (time-based)
Data transfer charges for IPsec egress traffic (usage-based)
Let’s dive into each item and understand what they are and what drives their cost.
VPN Gateway Charge
Google charges for each VPN gateway you have based on the number of tunnels you have attached to that gateway. A tunnel in this case is a secure connection that is established between a VPN gateway, and another VPN gateway associated with a different private network (which could be another GCP VPC or a non-GCP private network, such as an on-premises office network). Additionally, Google will not bill for tunnels if they are in certain states (for example, a tunnel is not billed while it is in a provisioning or deprovisioning state).
For each tunnel, Google charges an hourly fee that is based on the Google Cloud region in which the VPN gateway is located.
Google also offers what it calls “high availability‚ (HA) VPN gateways. These gateways have a 99.99% availability SLA, but require a pair of tunnels to be set up on each gateway. This means that if you are connecting two VPCs together, you will need a total of 4 tunnels (2 tunnels attached to each HA VPN gateway in each VPC). Each HA VPN gateway must also be in the same Google Cloud region.
Each VPN tunnel: $0.05 to $0.075 per hour
Non-tunnel External IP Addresses
Google also charges for each external IP address assigned to a VPN gateway, but only if the IP address is not used as a public IP address for a Cloud VPN tunnel. (Google also does not charge for static external IP addresses that are assigned to forwarding rules that send traffic to the VPN gateway.)
For each external IP address, Google charges an hourly fee that is based on their standard external IP address pricing, which is:
Static and ephemeral IP addresses used on standard VM instances: $0.004 per hour
Static and ephemeral IP addresses used on preemptible VM instances: $0.002 per hour
Preemptible VM instances are cheaper VMs that use excess Compute capacity within Google Cloud, but are subject to being stopped if the excess computing power is needed by standard VM instances.
Currently, charges are the same regardless of the region that the VPN gateway is located in, but Google may introduce differentiated pricing in future. In summary:
Each non-tunnel external IP address: $0.002 to $0.004 per hour
Egress Data Transfer Charges
Google charges data transfer fees for egress traffic (traffic exiting a VPC via a Cloud VPN gateway). Two pricing schemes exist depending on the destination of that traffic: outbound traffic destined for another Cloud VPN gateway uses VM-VM egress pricing rates, and outbound traffic destined for a VPN gateway outside of Google Cloud uses internet egress pricing rates. Fees are attributed to the project of the VM that is sending the traffic.
If the source and destination Cloud VPN gateways are in the same Google Cloud region, egress traffic is billed as traffic between zones in the same region.
VM-VM egress pricing: VM-VM traffic is priced on a per GB basis, and the rate is determined by the region of the source VPN gateway and the region of the destination VPN gateway, as well as whether internal IP addresses or external IP addresses are being used. (Note that the IP address of the destination VPN gateway determines the destination location, not the IP address of the destination VM a connection is ultimately intended for.)
Egress traffic is cheapest when it is sent to the same Google Cloud zone or region. Inter-regional egress traffic within the same continent is more expensive ($0.01 to $0.08 per GB), and intercontinental egress traffic is more expensive still ($0.08 to $0.15 per GB).
Amount of VM-VM egress data transferred: Up to $0.15 per GB
Internet egress pricing: Google offers two tiers of internet egress pricing - Standard and Premium (Premium is used as the default unless you specify Standard explicitly). Both tiers price using different approaches.
Premium Tier pricing charges a per GB rate which is based on: (1) the region the source VPN gateway is located in, (2) the location of the traffic’s destination, and (3) the aggregate monthly bandwidth used, with lower rates available with greater monthly bandwidth use.
For example, if you have a Cloud VPN gateway in the Las Vegas region (us-west4), the first 1 TB of egress traffic bound for Australia in a month is charged at $0.19 per GB, and the next 9 TB is charged at $0.18 per GB.
Standard Tier pricing charges a per GB rate which is based on: (1) the region the source VPN gateway is located in, and (2) the aggregate monthly bandwidth used, with lower rates available with greater monthly bandwidth use.
For example, if you have a Cloud VPN gateway in the Tokyo region (asia-northeast1), the first 10 TB of egress traffic in a month is charged at $0.11 per GB (regardless of destination), and the next 140 TB is charged a $0.075 per GB.
(As of the date of publication, we note there is an inconsistency with units in Google’s pricing page for the Standard Tier - it mentions that egress pricing is per GiB delivered, but the table and everywhere else on the page references GB, so we have assumed GB is the correct unit. GBs are smaller than GiBs.)
Amount of internet egress data transferred (premium tier): $0.08 to $0.23 per GB
Amount of internet egress data transferred (standard tier): $0.045 to $0.12 per GB
Google Cloud VPN Pricing Calculator
Because there are a lot of variables to account for when working out pricing, we’ve made this Google Cloud VPN Pricing Calculator to help you estimate the fees you can expect to pay for your Cloud VPN.
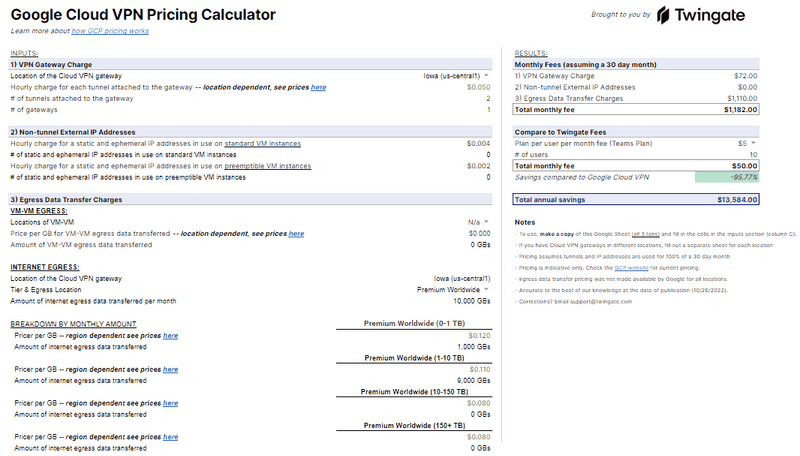
Google Cloud VPN Pricing Calculator
We note that pricing changes from time to time. The information in this article is accurate to the best of our knowledge at the date of writing, but you should check the Google Cloud website for the most up to date pricing.
Summary
Google Cloud VPN cannot be used as a P2S VPN server. If you use it as a P2P VPN server, the charges you can expect to pay for Google Cloud VPN include:
Hourly fees for each VPN tunnel attached to a Cloud VPN gateway
Hourly fees for each non-tunnel external IP address assigned to a Cloud VPN gateway
Bandwidth fees for egress traffic from the VPC the VPN gateway is located in
Alternatives to Google Cloud VPN
Google Cloud VPN is not your only option for establishing a secure way to access your GCP VPC environments. Moreover, one of the major limitations of Google Cloud VPN is that it cannot currently be used as a point-to-site VPN gateway that allows clients to securely connect into a GCP VPC.
Google Cloud Marketplace Products
The Google Cloud Marketplace contains a range of service providers who offer their own VPN software solutions that integrate with GCP. If you are looking for a P2S VPN gateway for Google Cloud, Google suggests in its documentation that customers may choose a marketplace vendor solution if a P2S VPN gateway is needed.
Each vendor offers their own pricing model, and a common deployment model is to offer VPN server software within a virtual machine (VM) that you can deploy into your VPC. OpenVPN Access Server is one such P2S-capable solution that is made available as an appliance. A subscription to the solution is purchased directly from OpenVPN and fees are based on the number of VPN connections needed, with a 5 connection minimum, and can be billed monthly or annually.
Manually Installed Products
On the other side of the spectrum, you could manually install and configure a software solution on a VM within your GCP VPC. Although there may be no software licensing fee associated with this route (such as for open source software) or perhaps a one-off payment for a perpetual license (for commercial software), it does require a lot more effort and expertise in terms of setup and maintenance. Additionally, support may not be provided, so you may have to seek third party help if you run into problems (either paid, or from free sources like community forums).
Zero Trust Alternative
If you are ultimately looking for a remote access solution, also consider Zero Trust Network Access products that aren’t based on VPN technology, such as Twingate. Twingate can be installed in a GCP VPC with a single line of code. Additionally, deployment can be automated in a variety of ways.
Another advantage of Twingate is that, unlike VPN technologies, there’s no concept of setting up site-to-site VPN tunnels to establish connectivity to your various network subnets. That reduces deployment complexity, as well as pricing complexity.
Zero Trust solutions have distinct security advantages over VPNs as well.
Twingate’s Pricing Model
A key benefit of using Twingate to secure remote access to your GCP environment is that the pricing model is straightforward. Twingate’s pricing is based on a per user flat fee model. That means costs are predictable - and you don’t need a spreadsheet to work them out!
The only variables that impact Twingate’s pricing are the number of users you have, the months or years you subscribe to the service (depending on whether you are billed monthly or annually), and the Twingate plan you select (Teams, Business or Enterprise). Subject to our Fair Use Policy, Twingate does not charge for bandwidth used or time connected. We even offer a free Starter plan if you want to try us out or if you only have a limited amount of infrastructure you need to secure.
If you use Twingate with non-GCP environments, support for GCP comes at no extra cost. In fact, Twingate secures access to all major types of environments (AWS, GCP, Azure, and on-premises) you may have for the same fee, and the setup process is similar for each environment.
Simplify Your GCP Secure Remote Access Needs
Twingate aims to provide the security benefits of a non-VPN Zero Trust solution while making deployment and management of that solution as simple as possible. Part of this is providing a simple to understand pricing model that won’t unexpectedly blow out your budget.
Contact us to learn more about how easy and cost effective implementing a modern zero trust solution can be.
Solutions
Solutions
The VPN replacement your workforce will love.
Solutions